Table of Contents >> Show >> Hide
- What Is the Bus Pirate 5?
- So What Does “Glitch” Mean?
- Why the Bus Pirate 5 Glitch Feature Is Interesting
- Inside the UART Glitch Demo
- The Hardware Features That Make This Practical
- What the Bus Pirate 5 Is Not
- Security Lessons for Embedded Developers
- Why Makers Should Care Even If They Are Not Security Pros
- Practical Bench Advice
- Experience Notes: What Working With a Bus Pirate 5 Glitch Setup Feels Like
- Conclusion
Note: This article is written for authorized hardware research, electronics education, and defensive security learning. Glitching should only be tested on devices you own or have explicit permission to evaluate.
The Bus Pirate 5 has always sounded like a gadget from a cyberpunk garage sale: part serial adapter, part logic probe, part tiny command-line wizard, and part “please do not cross these wires unless you enjoy smoke.” But the latest buzz around it is even more exciting. The Bus Pirate 5 can now be used as part of a glitching setup, turning a beloved embedded-hardware multitool into a practical learning platform for fault injection.
That does not mean it is a magical skeleton key for every chip on your bench. It means something more useful: the Bus Pirate 5 is becoming a friendly, affordable way to understand how timing, voltage, firmware behavior, UART interfaces, and weak security assumptions can collide in very interesting ways. In plain English, it helps you explore what happens when a microcontroller is nudged at exactly the wrong moment and accidentally does exactly what it was not supposed to do.
For hardware hackers, reverse engineers, students, makers, and embedded-security fans, that is deliciously nerdy news. For product designers, it is a reminder that “it works on my desk” is not the same thing as “it survives the real world.”
What Is the Bus Pirate 5?
The Bus Pirate 5 is a modern version of the classic Bus Pirate, a universal serial interface tool used to talk to chips without writing a custom program first. Instead of spinning up a microcontroller project just to test an I2C sensor, SPI flash chip, UART console, 1-Wire device, LED strip, or other digital interface, you connect the Bus Pirate, open a terminal, choose a mode, and start poking around.
That is the charm. The Bus Pirate is not trying to be a luxury oscilloscope or a full-blown commercial security lab. It is the pocketknife you reach for when you have a mystery chip, a handful of jumper wires, and a suspicious feeling that the datasheet is laughing at you.
The Bus Pirate 5 improves the formula with an RP2040 microcontroller, onboard storage, a color display, buffered input/output pins, voltage measurement on the pins, configurable pull-up resistors, and a programmable power supply. Those details matter because modern embedded hardware is a jungle of voltage levels, fragile pins, and “oops, that was 5 volts” moments. The buffered I/O and measurement features make the tool much more comfortable for day-to-day probing.
So What Does “Glitch” Mean?
In embedded security, a glitch is a carefully timed disturbance. Instead of attacking software with a password list or poking at a web form, glitching attacks the physical behavior of the device. The goal is to make a chip misbehave for a tiny slice of time.
That disturbance can happen in several ways. A voltage glitch briefly drops or disrupts the power rail. A clock glitch messes with timing. An electromagnetic pulse can induce a fault from outside the package. Optical fault injection can use light against exposed silicon. The common theme is simple: the attacker tries to make the target skip, corrupt, or misread an operation at the perfect moment.
Imagine a microcontroller checking a password. Under normal conditions, it receives input, compares that input to the stored password, rejects the wrong answer, and asks again. With fault injection, the experimenter tries to disturb the chip right when the comparison or branch decision happens. If the timing lands just right, the device might skip the rejection path or set a variable incorrectly. The result can look like a password bypass, even though the password was never known.
That sounds dramatic, and it can be. But in practice, glitching is usually more like fishing in the dark with a very tiny hook. The timing window may be measured in nanoseconds or microseconds. One setup may need hundreds or thousands of attempts. Move a wire, change a capacitor, warm the board, breathe too aggressively near the bench, and suddenly your “repeatable” attack develops a personality disorder.
Why the Bus Pirate 5 Glitch Feature Is Interesting
The exciting part is not that the Bus Pirate 5 replaces dedicated tools such as ChipWhisperer. It does not. The exciting part is that it lowers the educational barrier. Many people already use the Bus Pirate for UART, SPI, I2C, flash chips, sensors, smart cards, and board bring-up. Adding glitch-triggering capability to that familiar command-line environment makes fault injection less mysterious.
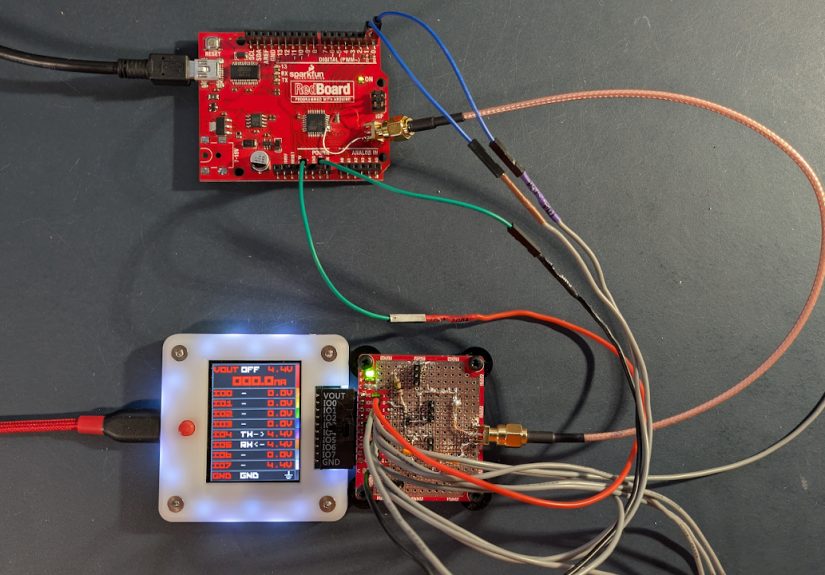
The official UART glitch demo focuses on an Arduino Uno target with a password-protected UART interface. The Bus Pirate handles timing and triggering, while external glitch hardware performs the electrical disturbance. This distinction is important. The Bus Pirate is not directly “zapping” everything by itself. It coordinates the moment when the glitch should occur, and the external circuit performs the actual power disturbance.
That architecture makes sense. In a typical voltage-glitch experiment, the control tool needs to watch or drive a communication line, identify the right moment, wait a defined delay, fire a trigger output, and repeat the attempt until the target behaves differently. The Bus Pirate 5 can sit in the middle of that workflow because it already speaks UART, has controllable I/O, and can operate from an interactive terminal.
Inside the UART Glitch Demo
The demonstration target is intentionally simple: an Arduino sketch asks for a password over UART. When the wrong password is entered, the device prints a familiar “please enter password” style prompt. When the correct path is reached, it exposes a small command prompt.
The glitching experiment takes advantage of the predictable timing between the entered character and the target’s response. First, a logic-analyzer view helps estimate when the password check is happening. Then the Bus Pirate sends the configured trigger character, waits a configured delay, activates a glitch output for a very short period, and reads the UART response. If the normal failure character appears, the attempt failed. If a different prompt appears, the glitch may have worked.
That loop is the real lesson. Glitching is not usually one heroic button press. It is a search problem. You search across timing delay, pulse width, target behavior, power conditions, and response parsing. It is less “Hollywood hacker montage” and more “spreadsheet meets solder fumes.”
In the demo, the target can be glitched into showing a command prompt instead of asking for the password again. That is a perfect teaching example because it compresses the core idea into something easy to understand: a weak authentication flow, predictable timing, unlimited retries, and a physical disturbance at the critical moment.
The Hardware Features That Make This Practical
The Bus Pirate 5’s hardware is a big part of why this is fun. Its RP2040 foundation gives it flexible timing options, and the buffered I/O helps it communicate with targets across common embedded voltage ranges. The tool’s programmable power supply is useful for ordinary hardware work, while current sensing and limiting help reduce bench drama. Nobody wants a learning session to end with the unmistakable scent of roasted microcontroller.
The live voltage information is also underrated. When working with unknown boards, being able to see pin voltages and confirm pull-up behavior directly from the tool saves time. It does not replace proper lab equipment, but it gives you immediate situational awareness. For glitching and reverse engineering, that matters because many failures come from boring problems: wrong ground reference, wrong logic level, floating lines, accidental back-powering, or a target that is not actually running.
The Bus Pirate 5 also starts in a high-impedance mode, which is a wise default. Hardware hacking already has enough opportunities for self-inflicted chaos. A safe initial state reduces the chance of driving a line before you understand what it is connected to.
What the Bus Pirate 5 Is Not
Let’s lovingly deflate the hype balloon before it knocks over the soldering station. The Bus Pirate 5 is not a push-button exploit machine. It will not automatically unlock random consumer electronics. It will not make secure chips collapse like a cheap lawn chair. It is also not a replacement for a high-end oscilloscope, professional glitching platform, or deep silicon security lab.
What it offers is a compact and approachable way to learn. For students, it demonstrates how physical behavior affects software assumptions. For makers, it reveals why “just compare the password and move on” is not always robust. For security engineers, it provides a low-cost way to demonstrate fault-injection concepts to teams that may otherwise think hardware attacks are exotic movie magic.
That educational value is huge. Many embedded products still expose UART consoles, use weak boot flows, rely on predictable timing, or assume attackers will never touch the board. The Bus Pirate 5 glitch workflow makes those mistakes visible.
Security Lessons for Embedded Developers
The biggest lesson is that authentication should not depend on one fragile branch. If a single skipped comparison can unlock privileged behavior, the design needs more defense. Good embedded security layers checks, limits retries, adds delays, avoids predictable timing, validates state transitions, and uses hardware security features where appropriate.
Retry limits matter. In the demo-style scenario, unlimited password attempts create a wide runway for experimentation. Add rate limiting, lockouts, randomized delays, and tamper-aware behavior, and the attack becomes much harder. Even small changes can move a target from “classroom demo” to “not worth casual bench time.”
Brownout detection and reset behavior also matter. If a device continues running in a half-confused state after a supply disturbance, it may expose strange behavior. A well-designed system should detect unsafe voltage conditions and reset cleanly rather than stumble forward like a sleepy raccoon operating a forklift.
Secure boot, debug-port locking, encrypted firmware, protected secrets, and careful error handling all contribute to resilience. None of these features is perfect alone. Together, they create friction. In security, friction is often the difference between a neat demo and a failed attack.
Why Makers Should Care Even If They Are Not Security Pros
Glitching teaches electronics in a memorable way. It forces you to think about timing, capacitance, power rails, UART framing, firmware control flow, and real-world noise. You stop imagining microcontrollers as perfect little logic angels and start seeing them as physical systems with thresholds, delays, and bad days.
That mindset helps with normal debugging too. The same person who learns to watch UART timing for a glitch experiment will also become better at diagnosing flaky boot behavior, unstable sensors, brownout resets, and “works when USB is plugged in but not on battery” mysteries. Glitching is security-flavored, but the skills transfer to ordinary embedded development.
The Bus Pirate 5 is appealing because it brings many of those observations into one workflow. You can talk to a device, measure lines, change modes, observe logic, and coordinate experiments from a terminal. It feels less like assembling a lab from scratch and more like expanding a tool you already understand.
Practical Bench Advice
Start with a sacrificial target. An Arduino Uno, spare ATmega board, or intentionally vulnerable demo device is perfect. Do not begin with your car’s ECU, your smart lock, your work laptop, or anything that would make a lawyer appear from the ventilation system.
Use a current-limited supply. Keep grounds common. Label wires. Record settings. Change one variable at a time. If an attempt succeeds, do not immediately declare yourself the emperor of fault injection. Repeat it. Then repeat it again. Glitching is noisy, and one lucky result can fool you.
Expect failure. In fact, expect failure to be the default state. Successful glitching often requires patience, careful timing, and a willingness to inspect what the target is actually doing. A logic analyzer trace can save hours of guessing. A clean wiring setup can save your sanity. A notebook can save you from rediscovering the same bad setting six times, which is the hardware-hacking equivalent of stepping on the same rake while maintaining eye contact with it.
Experience Notes: What Working With a Bus Pirate 5 Glitch Setup Feels Like
The first experience most people have with a Bus Pirate 5 glitching workflow is not instant success. It is curiosity followed by confusion, followed by a small victory that feels wildly out of proportion to the number of jumper wires involved. You connect the target, open the terminal, confirm UART communication, and for a moment everything feels civilized. The target prints a prompt. The Bus Pirate responds. The bench is calm. Then glitching enters the room wearing muddy boots.
The real work begins when you try to understand timing. You are no longer just sending characters; you are asking, “What exactly happens after this carriage return?” That question changes the way you look at firmware. The password check is not an abstract line of C anymore. It is an event that happens after a measurable delay, between observable UART transitions, while the microcontroller is executing instructions and relying on stable power. Suddenly, software has a physical shadow.
A common beginner mistake is treating the glitch as a single magic number. Set the delay, set the pulse width, press go, wait for victory. In reality, the useful window may be narrow, inconsistent, or affected by the target’s power network. Add decoupling capacitors and the pulse may be swallowed. Use long wires and the waveform may look like spaghetti having an argument. Use a weak MOSFET setup and the voltage dip may be too gentle. Use too aggressive a setup and the target resets instead of misbehaving. There is a surprisingly poetic difference between “skip this instruction” and “fall over completely.”
The Bus Pirate 5 helps because it keeps the experiment approachable. You can stay in one terminal environment, verify the UART link, trigger attempts, and observe responses without constantly changing tools. That does not remove the need for good lab discipline, but it reduces the amount of ceremony. The experience feels like learning by conversation: ask the target a question, disturb it at a chosen moment, listen to what comes back, adjust, and try again.
When the first successful glitch happens, it is easy to overreact. The prompt changes, the response is different, and suddenly the target appears to have skipped a rule. That moment is fun, but the better lesson comes afterward. Why did it work? Was the timing stable? Was the result repeatable? Did the device skip a comparison, corrupt a variable, or reset into a strange state? Could a defender prevent this with retry limits, randomized timing, brownout reset configuration, or a stronger authentication design?
That is the best part of the Bus Pirate 5 glitch story. It turns fault injection from an intimidating specialist topic into something you can reason about on a modest bench. You come for the cool trick. You stay because it makes you better at understanding embedded systems.
Conclusion
The Bus Pirate 5 sure can glitch, but the headline is bigger than a clever demo. It shows how a flexible serial-interface tool can become a practical gateway into fault injection, hardware security, and deeper embedded debugging. By combining UART control, timing, I/O handling, voltage awareness, and an approachable terminal workflow, the Bus Pirate 5 makes a complex topic feel less like dark magic and more like a disciplined experiment.
For hackers and makers, it is a fun new capability. For engineers, it is a warning label with a USB-C port: predictable timing, weak password handling, unlimited retries, and poor voltage-fault behavior can become real vulnerabilities. For educators, it is a compact way to demonstrate why hardware and software security must be designed together.
The best use of this feature is not breaking things for bragging rights. It is learning how devices fail, how attackers think, and how better products are built. That is where the Bus Pirate 5 shines: not as a magic wand, but as a delightfully nerdy flashlight pointed into the messy, fascinating space between code and physics.